The term Ledger Live Login is commonly searched by users who want to access their crypto portfolio securely. This page provides a complete educational explanation of how Ledger Live access works, what users should expect, and how to stay safe while managing digital assets. 🚀
What Is Ledger Live? 💡
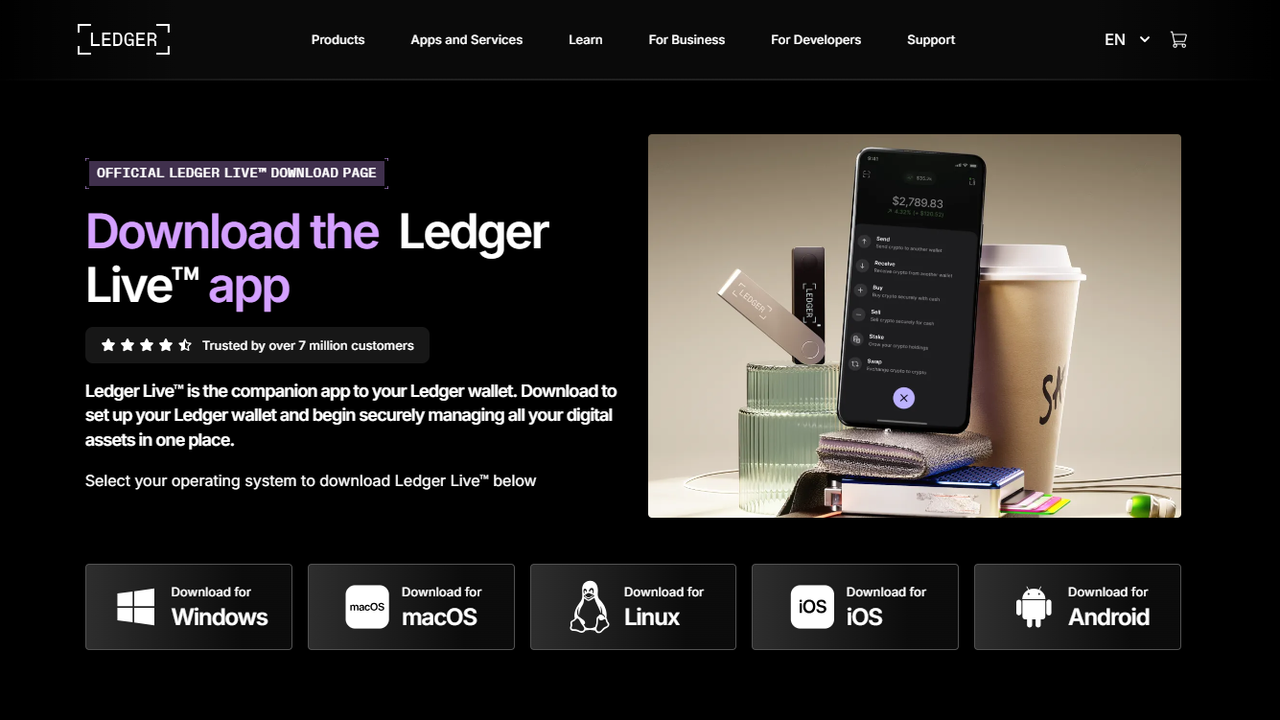
Ledger Live is a companion application designed to work with Ledger hardware wallets. Unlike traditional online wallets, Ledger Live does not store private keys on servers. Instead, private keys remain securely inside the hardware device. This design significantly reduces exposure to online threats.
Ledger Live allows users to view balances, install blockchain apps, send and receive cryptocurrencies, and monitor transactions — all while requiring physical confirmation on the hardware wallet.
Understanding the Concept of “Login” 🔍
Many users search for “Ledger Live login,” but Ledger Live does not function like a typical username-and-password platform. There is no web-based account login system. Instead, access is controlled through the physical Ledger device itself.
When users open Ledger Live, they connect their hardware wallet and confirm actions directly on the device screen. This ensures that even if a computer is compromised, transactions cannot be approved without the physical device.
Why Ledger Does Not Use Traditional Logins 🛡️
Traditional login systems rely on centralized databases that store usernames and passwords. These systems are vulnerable to breaches and leaks. Ledger avoids this risk by eliminating centralized authentication entirely.
Instead of a login, Ledger Live relies on:
- Physical device confirmation
- User-generated PIN codes
- Offline private key storage
- Manual transaction approval
Common Login Scams to Avoid 🚫
Because users search for “Ledger Live login,” scammers sometimes create fake websites that mimic official pages. These malicious pages often request recovery phrases or PIN codes.
Always remember:
- Ledger will NEVER ask for your recovery phrase
- No legitimate Ledger login page exists
- Recovery phrases should only be written offline
- Browser pop-ups asking for seed phrases are scams
How Secure Access Actually Works 🔑
Access to Ledger Live is secured through device authentication. When you connect your Ledger hardware wallet, the application checks the device and waits for confirmation before allowing sensitive actions.
Each transaction must be verified on the device screen, ensuring that no unauthorized action can occur without your physical presence.
Recovery Phrase: Your True Access Key 🌱
The 24-word recovery phrase generated during setup is the true key to your wallet. It is not a login password and should never be entered into any website or app claiming to be Ledger Live.
This phrase should be stored securely, offline, and protected from fire, water, and theft. Anyone with access to this phrase can control your assets.
Device PIN vs Online Password 🔐
The PIN code used on Ledger devices protects against unauthorized physical access. If the device is lost, the PIN prevents immediate access to funds.
Unlike online passwords, the PIN is verified locally on the device and never transmitted over the internet.
Best Practices for Staying Safe 🧠
- Bookmark official websites instead of searching
- Never trust ads claiming “Ledger login” pages
- Update Ledger Live only through official sources
- Keep your operating system secure
- Verify transaction details on the device screen
Educational Summary ✅
The idea of a “Ledger Live login” can be misleading. Ledger’s security model is intentionally designed to avoid traditional logins and centralized access points. This approach gives users full control over their digital assets while minimizing attack surfaces.
Understanding how Ledger Live works helps users avoid scams, protect their recovery phrase, and manage crypto safely. Education is the first layer of security. 🌍